UPDATED 5/3/2017
This phishing scam has been making the rounds again today. Similar to the scam described below, this version appears as if someone you know has given you access to a Google document. In this case, the link is an actual app and by clicking it you give it access to your Google account. Do not click that link!
Here’s what it looks like – and yes, this is from my own in-box!
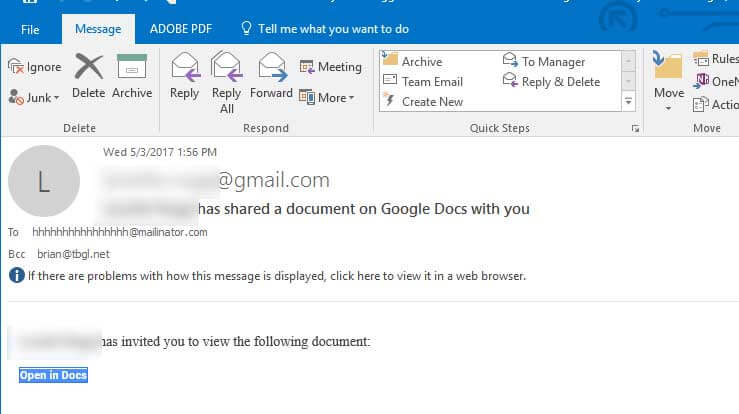
Here is what to do if you got caught by the latest Gmail phishing scam:
Go to https://myaccount.google.com/permissions to actively revoke access to the the malicious app from your account.
Click on all apps in the list, especially any that are listed for today or whatever date you clicked on the email.
Good luck!
Original Post, January 2017
As Gmail has over 1 billion active users, odds are that you have a Gmail account so you need to be aware of a new security threat.
Last week website security firm Wordfence called attention to a new phishing scam hackers are using that is fooling even the most experienced Gmail users. It is very convincing – in fact recently I almost fell for it myself! Here is a quick rundown of what the scam looks like and how you can avoid falling victim to it yourself.
What does the scam look like?
The basic scam is as follows:
- A hacker sends and email to you, most-likely using an email address of someone you know.
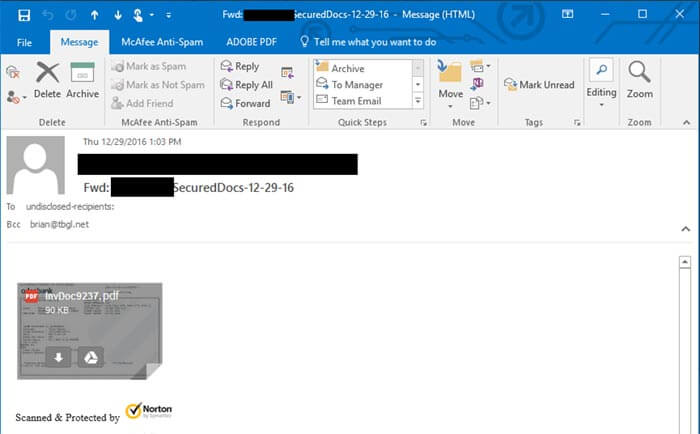
- Included in the email is an attachment that looks like an image of a document. Below you can see a screen shot of the email I received.

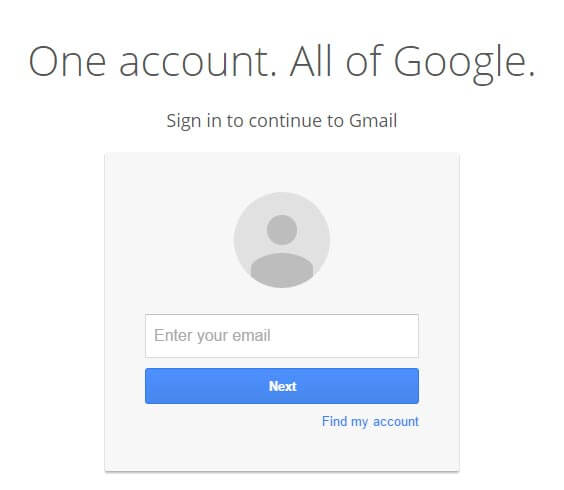
- When you click on the attachment you generally would expect a preview of the document. Instead, you are taken a Gmail login page.
- Assuming you were somehow logged out of Google, you sign in again.
- The email, document and login page are all fake. If you log in the hacker will immediately access your account, your emails and your contacts.
What makes this phishing technique so effective is that both the login page and even the URL displayed in your browser appear to be genuine.
Here is a screen shot of the login page, which is almost identical to actual Gmail login page:
Here is a screen shot of the URL in the browser; note that it includes “https://accounts.google.com/ServiceLogin?” which is the used in the real Gmail login URL.
With a genuine looking login screen and a URL that looks legitimate at a glance, no wonder so many people are being fooled.
How do I avoid this scam?
As I mentioned earlier, I almost fell for this scam. Only the fact that this person had no reason to send me an attachment and a touch of paranoia saved me. Here’s what to do:
- Check the URL field to verify the login link. It should start with https://accounts.google.com/ – there should be nothing in front of the padlock, the word “Secure” and the “https://”. If you take another look at the screen shot above you will notice the additional text in front of the https://, which is part of how the hackers make the scam work.
- Click in the URL field of your browser and drag to the right. As you drag you will find a long string of additional text after the URL. This is a script the enables the hacker the generate the false login page.
- Look for the word “Secure” and a green padlock. Google recently changed how it labels the security status of website login pages. If you don’t see these in the browser then it is not a legitimate URL and you should not click on it. Reference the screen shot below.

- To further protect yourself, consider setting up two-factor authentication. This requires a password and a code texted to your phone to gain access to your Gmail.

Brian Rugg
Vice President, Think Big Go Local, Inc.